GoPhish setup tutorial
Created on Sun. 16 Oct 2022
In this blog post we will cover how to setup gophish and evilginx using docker to deploy everything in a simple environment. I did the TCM Academy gophish and evilginx2 certification a few months back and got inspired to set it up inside of a docker environment to simplify the deployment of everything as much as I could.
Seeing at my last job I was used to use gophish for an engagement I thought it was about time that I wrote this blog post. To quickly go through the environment is setup in such a way so that it can be easily deployed in around an hour with evilnginx2 resetting on reboot but gophish email config persistent. I didn't really choose who was persistent or not it just somehow happened :)
Dependencies
To have everything setup correctly you will need a few dependencies and you will need to edit a few configurations to avoid things crashing into one an other. Because gophish and evilnginx both log everything to stdout just make sure you have tmux installed on your server.
# apt install tmux
Note that I am using vultr as my server provider with the docker server config for ease of use but it can also be done on other cloud providers like AWS for example.
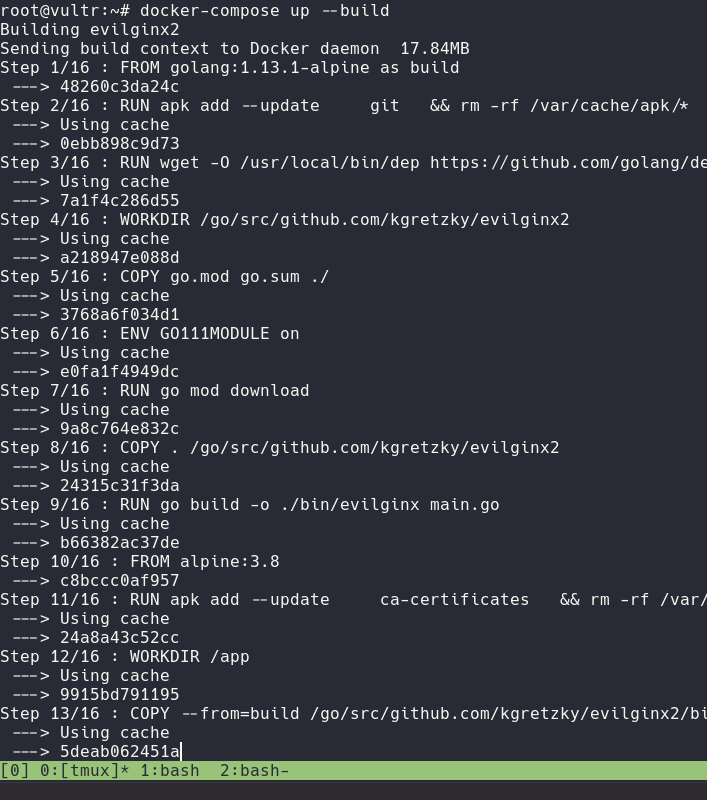
After installing tmux we will now have to download a docker-compose file which contains information on the config of the server. This file can be found here.
Inside this file you can see that I put a few comments to help with the ease of use of the docker file. After getting that file on the server we then need to clone evilginx2 and delete the entry point inside of the Dockerfile this is done so that docker-compose just builds evilginx and does not run it. Docker-compose does not really have tty support so we will run that on our end.
# git clone https://github.com/kgretzky/evilginx2 && sed -i \$d evilginx2/Dockerfile
After this we are basically done and we can start setting up all of the services :)
Setup
We will first start by setting up gophish. To do that run tmux and launch the docker-compose inside of it:
On the output of gopish you should see that the service is running on https://localhost:3333 with a default admin password setup. Save that password you will need it. We then want to detach from the tmux session and logout of ssh to log back in with this command:
$ ssh @ -L 3333:localhost:3333
Replace user and ipaddr with the relevant information. We are basically doing a port forward through the ssh tunnel so that the gophish admin panel is not publicly exposed which would be a problem for us. You can now navigate on your browser to https://localhost:3333 and login and change your admin password. It should be prompted on first login :)
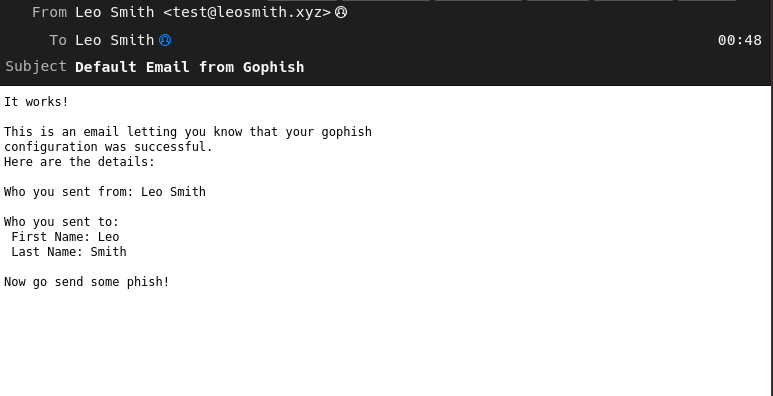
From there we can setup the smtp credentials to the stmp service of your choice. In this case I will be using my personal server.
If setup correctly you should receive a test email looking like such:
From here we can finally start setting up evilginx2 which only takes a single command. Navigate back to the tmux instance on the server and create a new pane and run the following command:
# docker run --user root -p 80:80 -p 443:443 -p53:53/udp -it root_evilginx2 /app/evilginx
You can now do all of the fun stuff with evilginx2 which will allow you to steal accounts pretty easily :)
Now this blog post does not cover all of the setup like DNS and such you do need previous experience with gophish and evilginx2 but at least with my docker-compose it removes most of the grunt work.
Categories
Book a phishing campaign

You can book a phishing campaign from me on your organisation by contacting me.
LinkedIn or twitter / X. I also use twitter as a platform to update on new posts!Questions / Feedback
Donate

If you like the content of my website you can help me out by donating through my github sponsors page.