Hunting IDOR during recon with BurpSuite
Created on Thu. 14 jan 2021
Before anything, HAPPY NEW YEAR :) I haven't been active on my blog for a while I had a lot of school work to catch up and a lot of freelance work to pay my bills :c. With that out of the way what is a better way to start the new year with a quick tutorial on how to use Burp Suite for IDOR hunting during recon!
With my new job as a bug hunter at Synack Red Team I started doing a lot of cool stuff to learn Web App pentesting a lot more deeply. I am still currently trying to master the OWASP Top 10 and one of the bugs I have been mostly focusing on are IDORs.
What are IDORs?
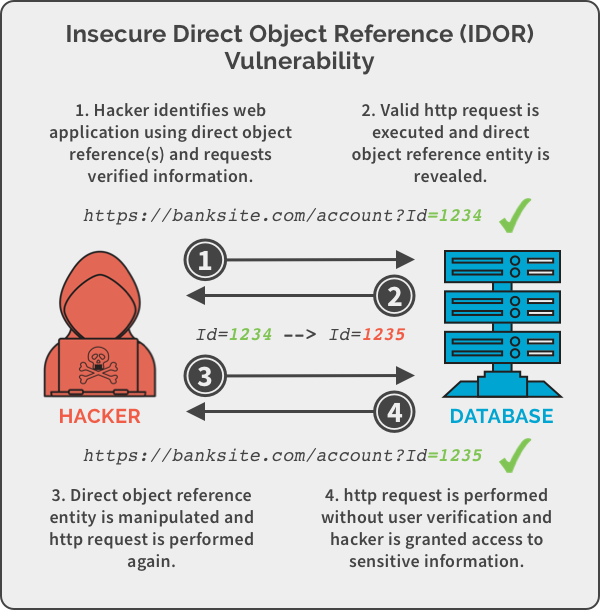
To get this out of the way if you are totally new to this IDORs or (Insecure Direct Object References) are a type of bug where you User A try to do actions that only User b is allowed to do. Here is a little image to demonstrate the vulnerability.
Installation
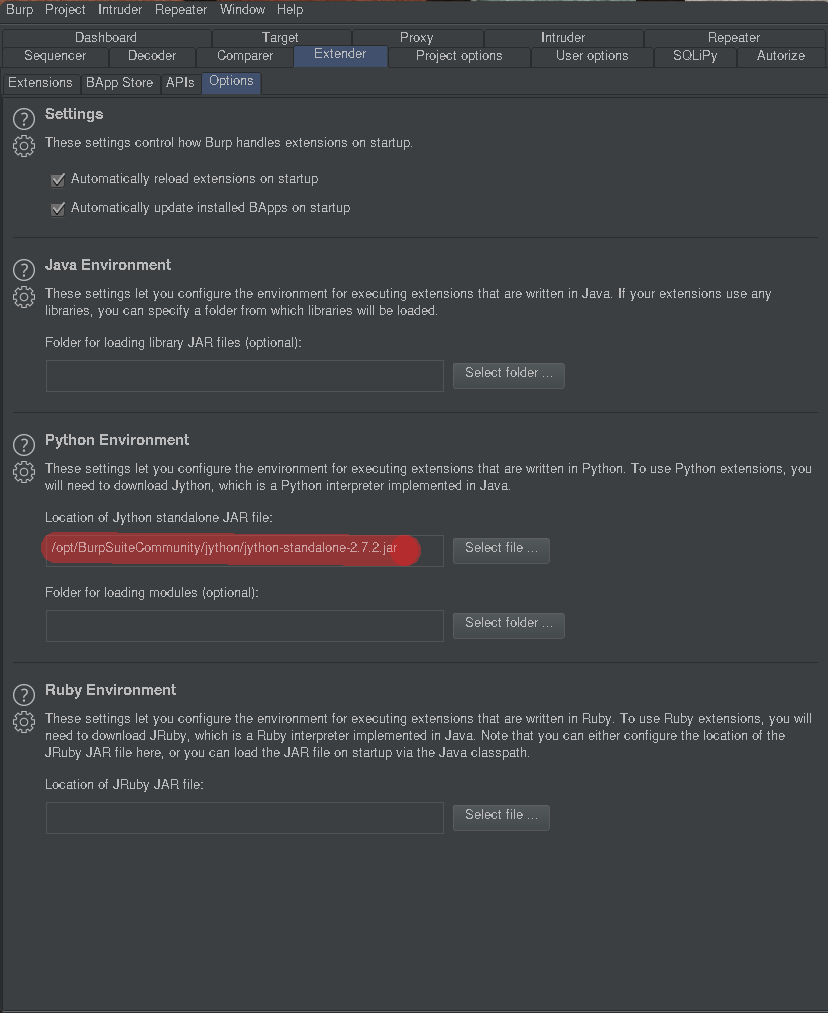
To start, you first need to setup BurpSuite to use plugins inside of it. To do that you need a copy of Jython, the Java interpreter of python. You can download it here.
After downloading jython you need to open Burp suite and navigate to Extender>Options>Python Environment and place the path to the file there.
You then need to install the plugin itself to find IDORS. You can find them manually but this tutorial is focused on automation ;). To install the plugin navigate to Extender>Bapp Store and install the Authorize plugin.
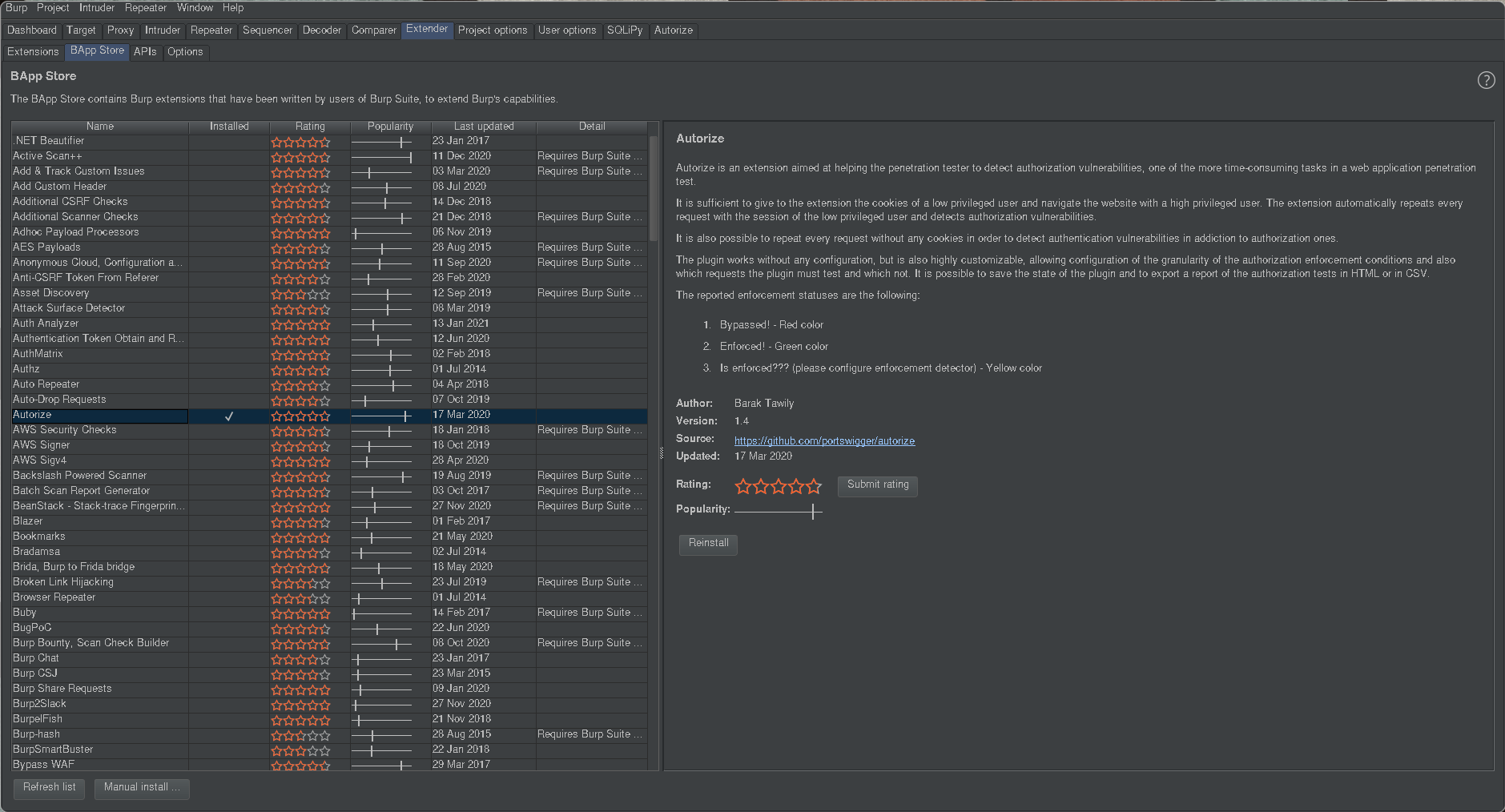
You should now have the plugin at the end of the top bar of BurpSuite, if it does not appear just restart BurpSuite. All of the plugins you install will be persistent even if you do not have BurpSuite pro.
Overview
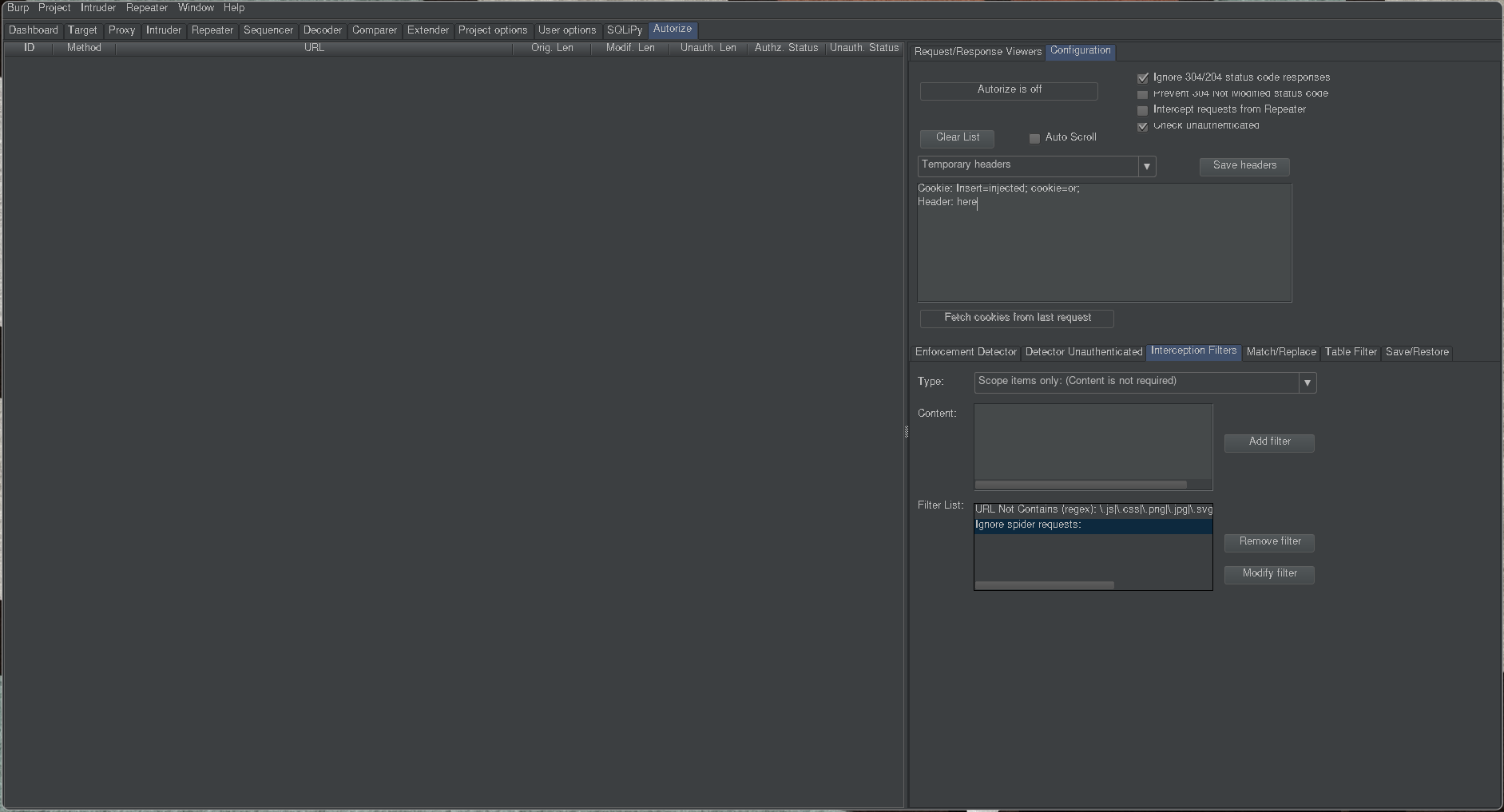
The first thing to keep in mind when using this plugin is that you need to activate it and configure it so that it actually repeats each request with different id's. So when you are using it just check the button that Authorize is in fact on. The second thing you need to configure is to put a header with different cookies than the one you are logged in as, maybe a lower privilege user if you have access to that will always be my go to for the headers section. I then usually add the scope only filter by clicking the Add filter button, the scope only filter is selected by default.
Usage
After setting up BurpSuite you now can start your normal process of recon by running around the app and using every functionality you can keep an eye on the authorize window to see if everything is working the way it should, the window should look something like this:
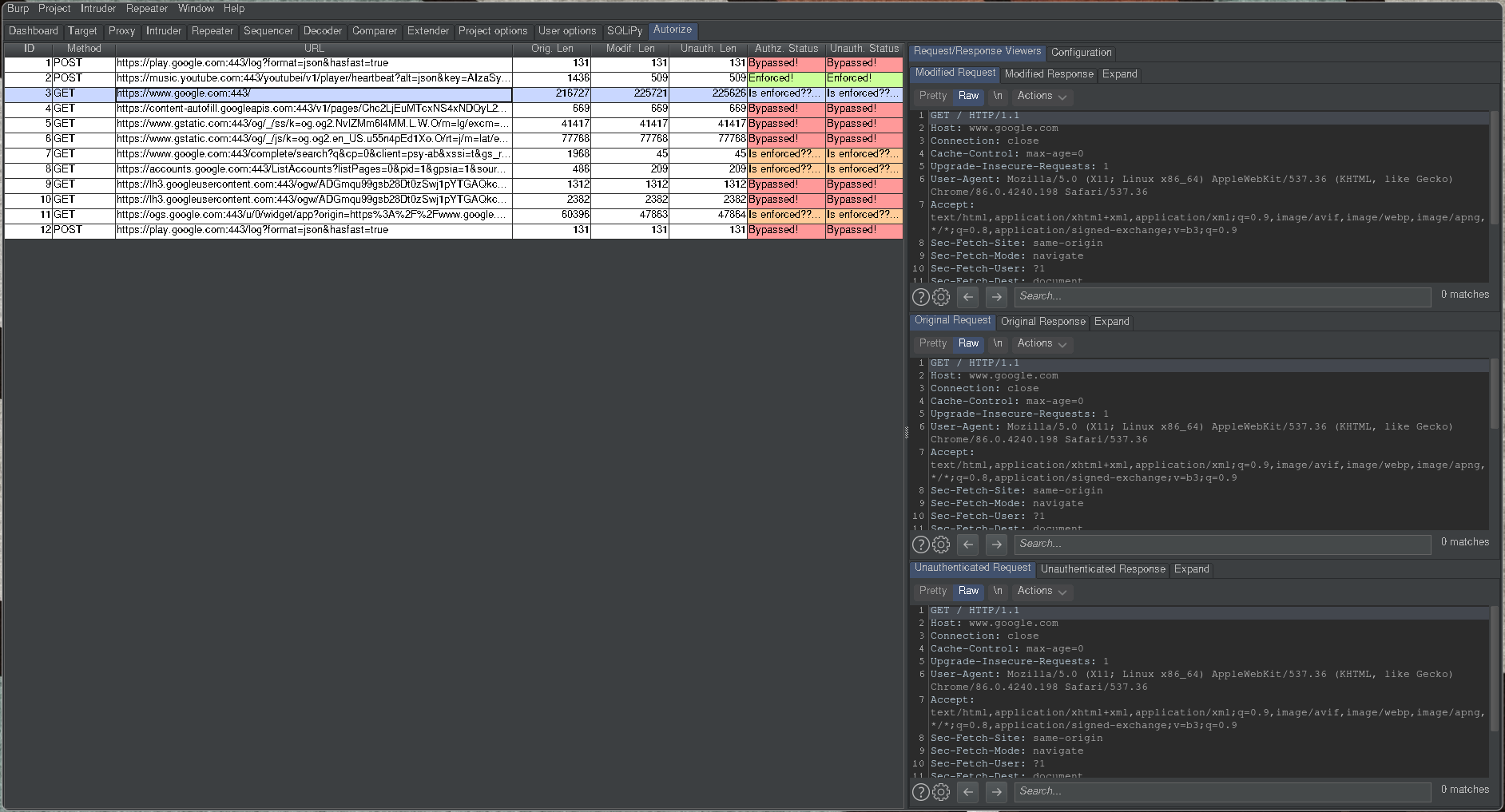
To the right of each request you can see colored boxes, those boxes are what is going to notify you of an IDOR if there is one. In green or Enforced means that the application is returning something totally different for each requests. The orange status or Is enforced?? is when the result is a little different the server didn't return a 401 error code and sent something but the result is different from the original request, for those one you might need to investigate a lot further to find IDORS. The last status that your will see is the red one or Bypassed! those request are the ones when the result is the same as the original one, in some cases this is good news :)
In Practice
Honestly this is my most used BurpSuite plugin I use it every time I go through a website even if I don't have an other account just to see what I could potentially do as an Unauthenticated account I was able to find 2 or 3 dupes with this method for now nothing impressive but i have been doing Bug Bounty for only a month now even if I joined synack 3 month ago now I was overwhelmed with school and stuff :c
Thank you for reading this and have a good day/night :)
Categories
Inspiration for this blog post
Questions / Feedback
Donate

If you like the content of my website you can help me out by donating through my github sponsors page.