Wifi Pineapple Evil AP
Created on Tue. 09 aug 2022

I'm back. It's been a while I needed a break a think a lot of crazy shit been going down in my life but it's nice to get back into pentesting. This post is basically an old attack that I did a few months back for college and is very simple with the wifi pineapple mark VII to do.
For this you will obviously need a Wifi pineapple mark VII to set that up you can follow the Hak5 tutorial for it.
Evil AP attack
The evil AP attack is basically an attack where you setup and AP with the same SSID and BSSID of an other wifi and use that to capture half the handshake to crack it on your machine to then connect to that wifi. This attack allows to crack mainly WPA2 & WPA this is what I would use it attack.
Recon
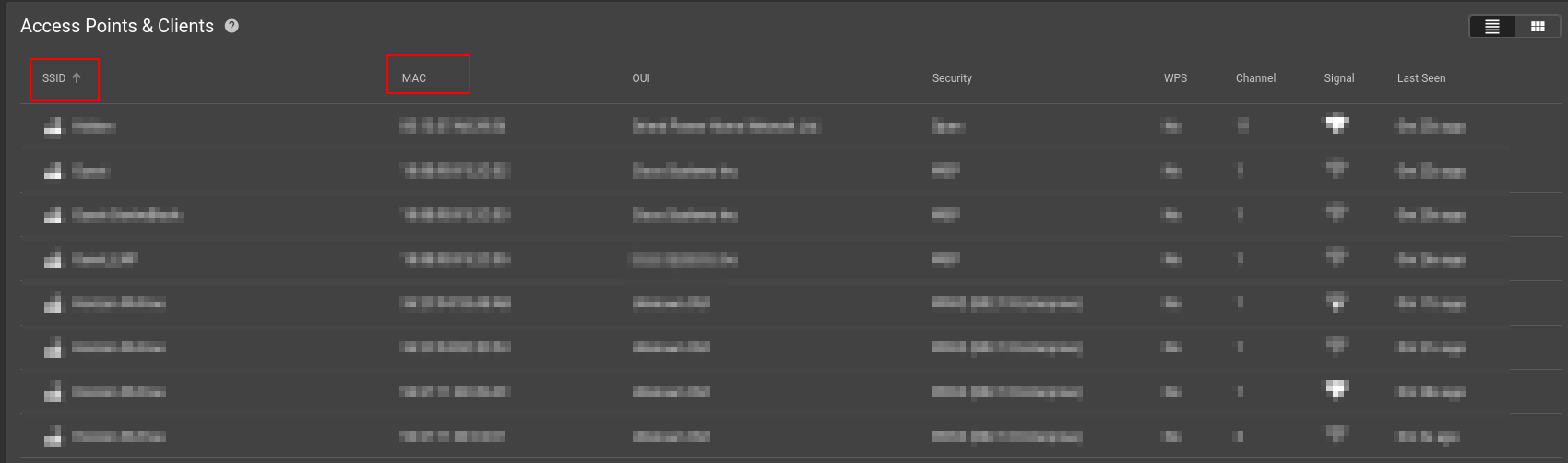
Usually you have a wifi to target for this attack so lets pick one of my old wifi so I can nicely disclose one of my last addresses :). The wifi we will clone is PP11_Flat7 with a BSSID of 46:4a:fb:8d:ca:b8. You can also use the wifi pineapple recon to catch a wifi around you to then clone that.
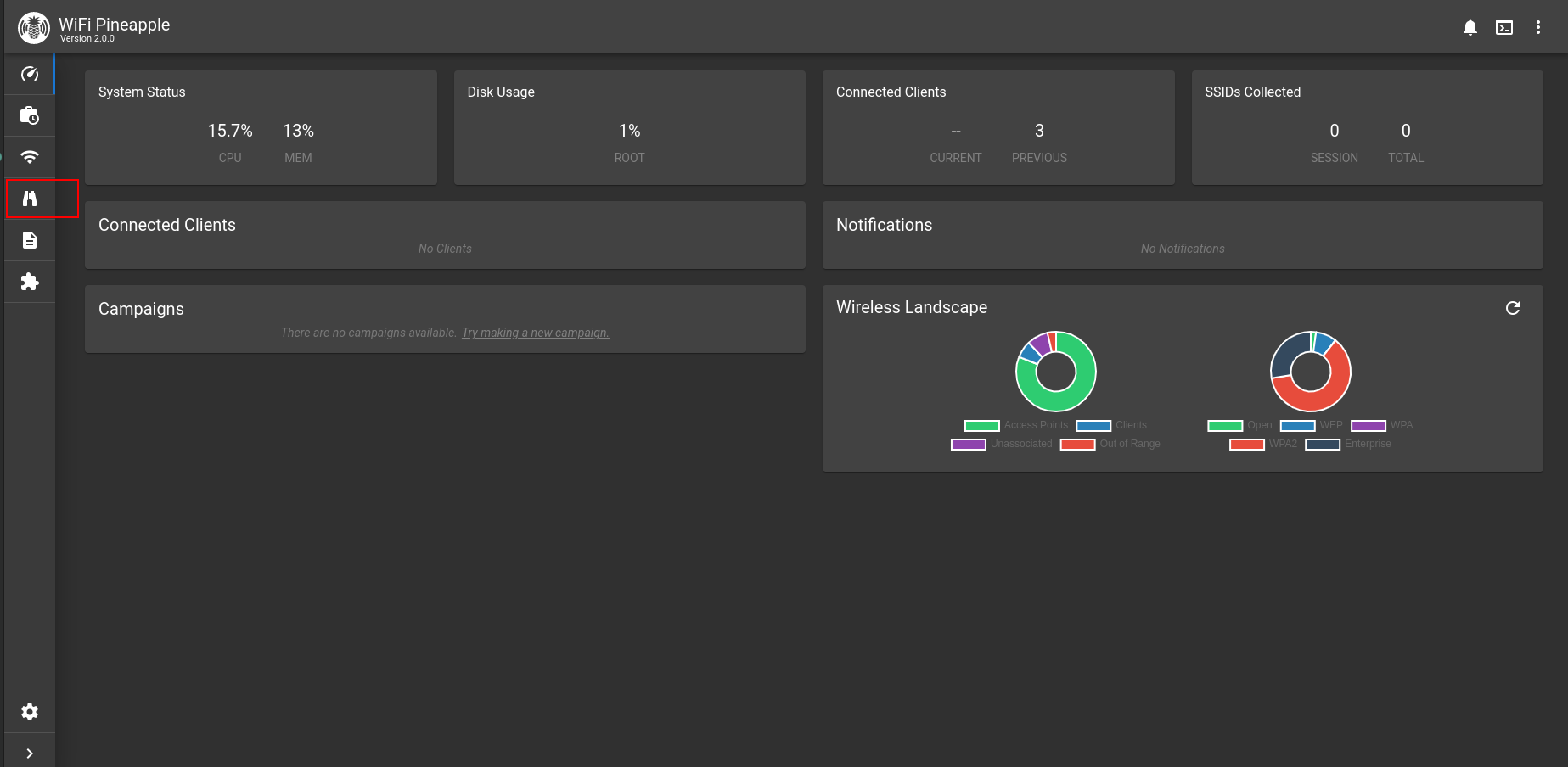
Navigate to the left panel and select the little binoculars that's the recon section. After starting it there are two columns that are needed to be written down SSID and MAC.
Exploitation
After getting the information of the wifi you want to clone you then need to navigate to PineAP Suite/Evil WPA
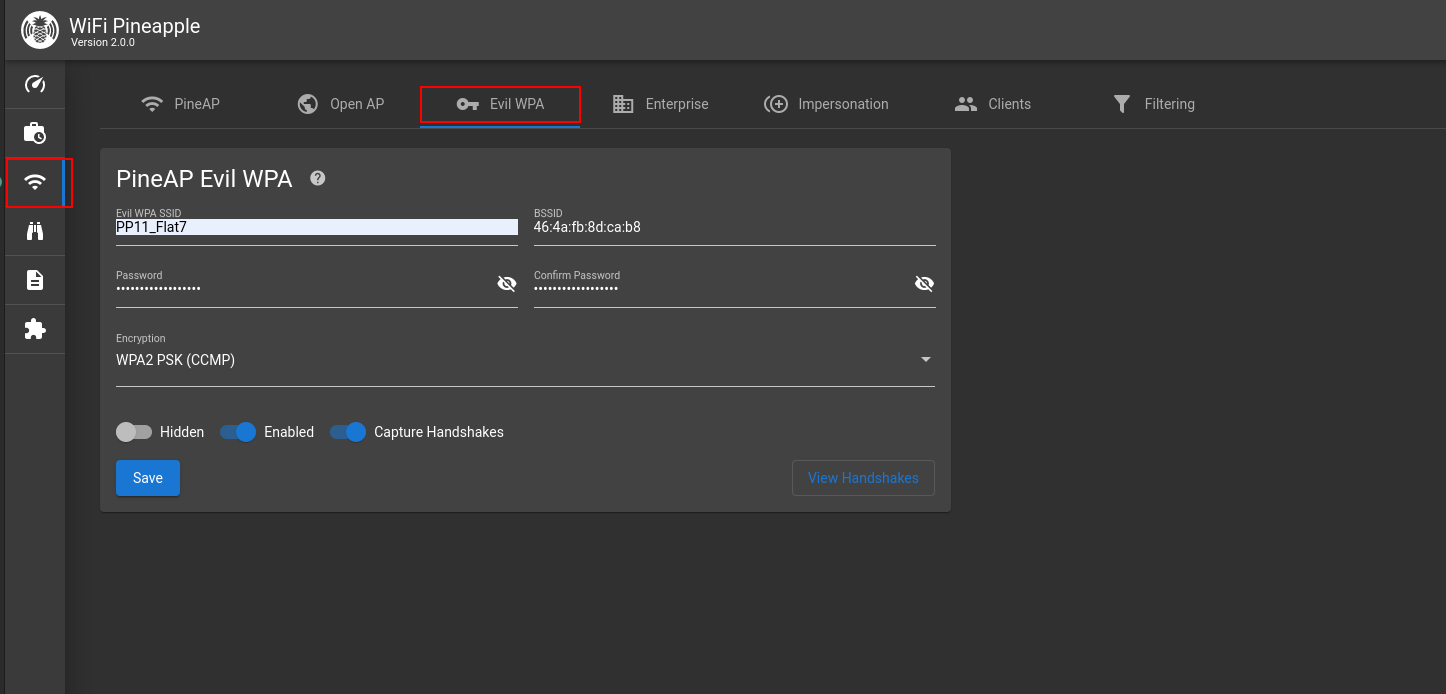
Inside that section fill in the information and make sure that Capture Handshakes is enabled same for Enabled. Also the password section can just be anything you do not need to set a real password. I personally picked pineapplesareyummy
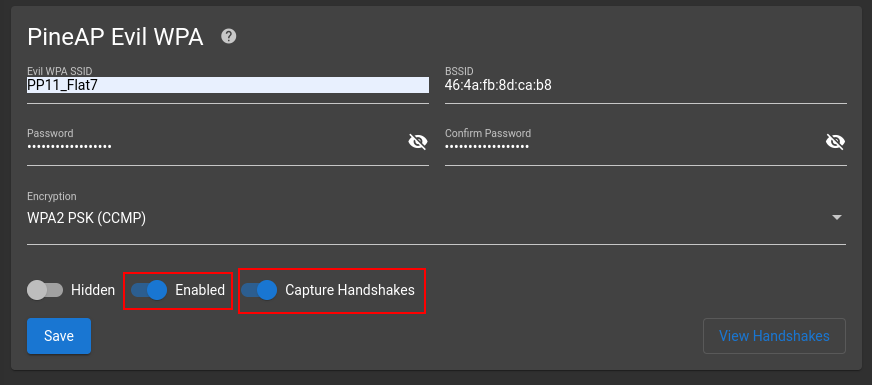
Now for this attack you can either de authenticate other clients to force them to connect to the wifi you are copying or you can just wait in the vicinity of the victim for their device to automatically connect. For example my phone will automatically connect to this wifi if it doesn't seen any one that are known to it. When a client connects the portal will notify you of a Handshake capture:

When a handshake is capture select the View Handshakes button. From there you should see a hashcat file and a pcap dump of the handshake. We will be using the hashcat file for the cracking.
Cracking
To extract the hashcat file you can use the scp command on your terminal or just ssh into the pineapple and copy paste the content of the file:
$ scp root@172.16.42.1:/root/handshakes/CHANGETORELEVANTMACADDR_eviltwin.22000 .
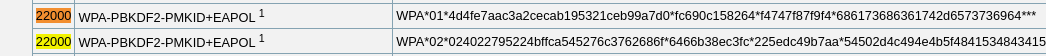
After extracting the hashcat file you can use the 22000 rule for cracking this file using a wordlist. Here is a screenshot of the hashcat documentation:
you can use the following command to crack the file:
$ hashcat -m 22000 ./CHANGETOMAC_eviltwin.22000 /path/to/wordlist
this command should produce the following output:
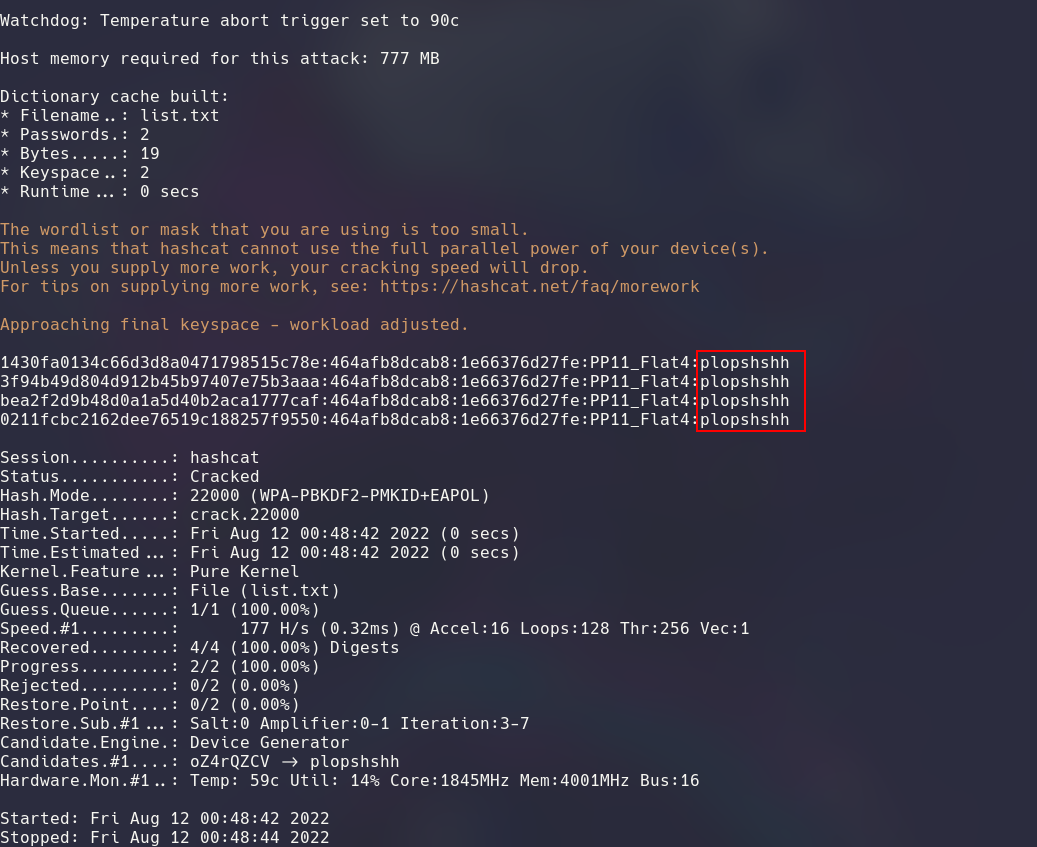
Now with that password you can connect to the wifi and start doing fun stuff :)
I hope not a lot of people follow this blog I am shit with dead lines and making regularly this kind of content. I prefer doing it as therapy for myself and to slowly build a backlog of my knowledge. This will now go to some personal stuff so if you don't care no need to read. I recently moved on from something big in my life and I think I really needed to do this i struggled all week to write this I am uploading this on a different date than what is written in the title and i am really not bothered to update it 😆. Take care I might do a second one tonight now that I'm in the mojo.
Categories
Links
Questions / Feedback
Donate

If you like the content of my website you can help me out by donating through my github sponsors page.