p3ng0s Release
Created on Sat. 04 Sept 2023
After doing a original blog post last year on September 28 on creating a custom arch linux iso that would incorporate all of my config for the past 6 Years of software development, linux hardening / configuring and obviously penetration testing. I finally have an actual distro to show.
I'm not going to lie between changing countries making new friends getting over multiple breakups and being stuck on how to use calamares (the installer I chose for my OS) the progress was quite slow. But I am satisfied to finally have something to showcase to you. Instead of explaining my decisions on the OS or what software is installed on how they are configured you can look at this blog post on more of a over view of what I did and you are welcome to go through the p3ng0s wiki directly and try it out for yourself.
Installing
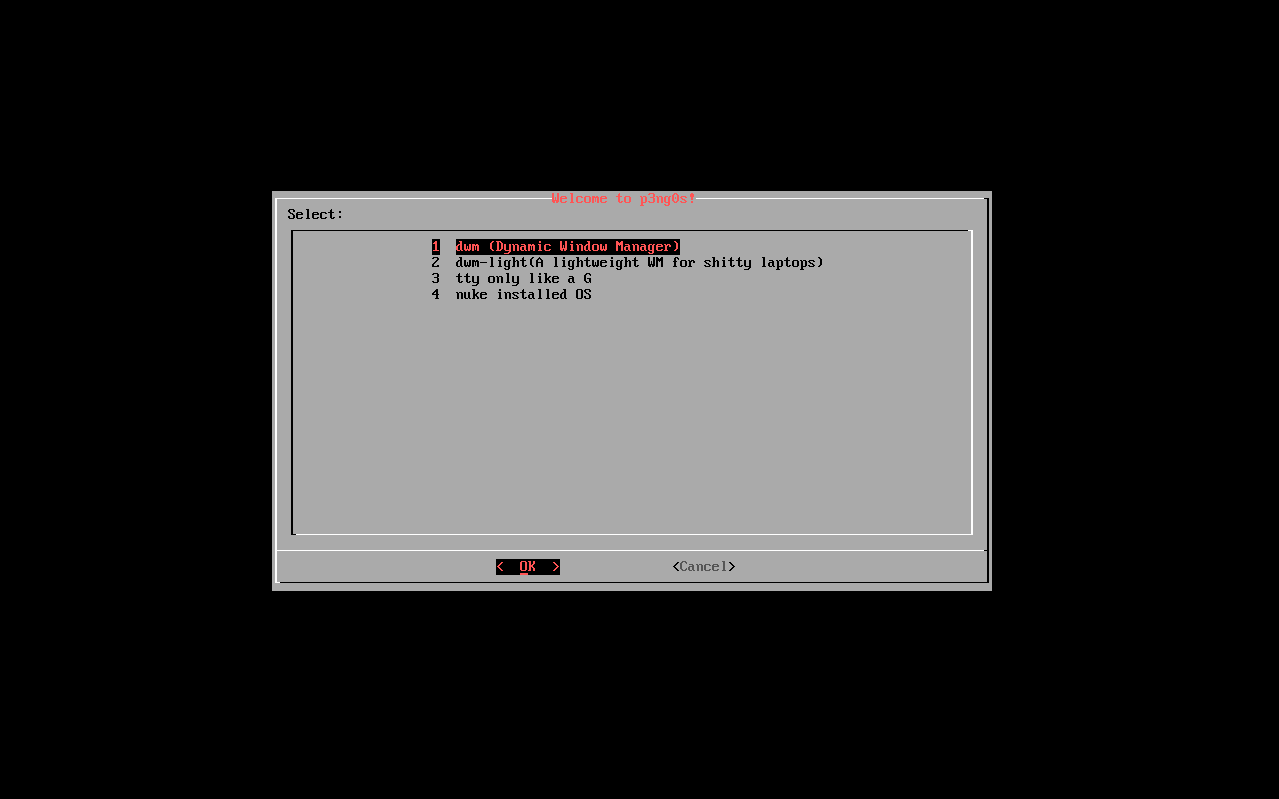
After navigating to the p3ng0s wiki and downloading the ISO you can just burn the ISO to a usb disk and boot from the disk. p3ng0s is a bit different since on initial boot you will be prompted with the OS killer menu which allows you to select a few options. If you just wish to install just select the 1st option dwm. From there calamares will be running on startup of the GUI environment.
If you wish to compile the ISO manually that is also possible using the build.sh script inside of the archlive repository in the p3ng0s official github. With the build.sh script you can modify it and add your own custom .bashrc .vimrc etc.. Directly to the created user inside of the live environment.

Manually building will take a good long time but it is great if you think the ISO is either too big or you want to add specific software to the default installation.
p3ng0s does also come with it's own "repo" now I do use that word lightly since it is not hosted in the cloud and is only local during the ISO build. But there you can find a few of the forks I use like the DWM fork, ST fork and such:

Features
The two main features that put p3ng0s apart from other operating systems is the fact that it comes with the os_killer.sh script which will allow you to do basic exploits on machines the USB key is plugged into. It also comes with a giant post install script called git_appocalypse.sh that will just install all of the dependencies and tools to do all of the work I need to do on a day to day basis.
git_appocalypse.sh
This sections is for redundancy but it's basically a giant git pull. You can refer to the source code here to see what is being installed.

os_killer.sh
Liked said previously this script is for attacking machines you are booting live from. If the hard drive is encrypted this tools will not be very useful but is still great just in case to have as a swiss army knife for not very secure computers. os_killer supports windows and linux operating systems, sorry I am never confronted to mac's but the day I will I'll add support I guess :/. Through the linux attacks you can either dump the shadow and passwd files for later cracking or ex filtration, or also chroot in the system to directly modify as root the structure of the OS. On the windows side you can either secretsdump the machine SAM, SYSTEM and SECRET from there maybe do a pass the hash attack. You can also just copy SAM, SYSTEM and SECRET for later ex filtration like on linux or you can also as a bonus copy cmd.exe as Utilman.exe to give you a backdoor directly as system on the login page if you really want to ^^.

Thank you so much for reading please do go on the p3ng0s wiki to discover more and I recommend you subscribing to either the RSS of this website or just following me on linked-in to see the cool stuff I do ^^.
Categories
p3ng0s
Questions / Feedback
Donate

If you like the content of my website you can help me out by donating through my github sponsors page.
